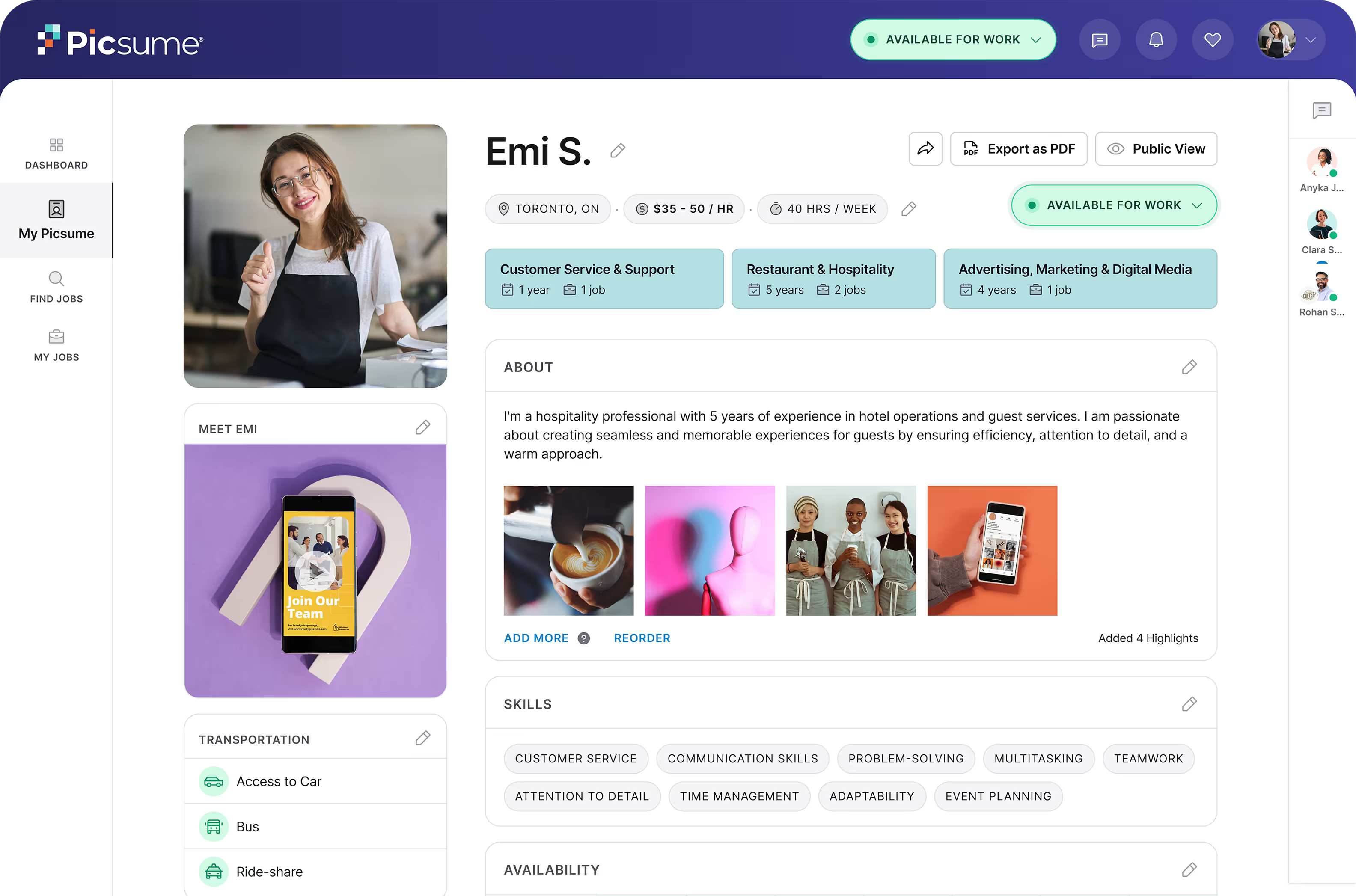
Built to protect your data. Designed for trust at scale.
Protected
Encrypted
Monitored
For Employers
What This Means for You
Secure & Private
Your data is kept secure and private with strong protections.
Controlled & Tracked
Access is controlled and tracked through permissions and logs.
Exclusive Access
Only your team can access your workspace information.
You Own Your Data
You retain ownership of your data, with privacy respected by design.
Infrastructure
Secure Infrastructure by Design
Picsume uses enterprise-grade cloud infrastructure with secure managed backend services and built-in frontend security.
- Encrypted data in transit and at rest
- Tenant-aware access controls
- Managed infrastructure with a reduced attack surface
- Platform-level protections and application-layer security
- Centralized logging and monitoring

Ownership
Data Ownership & Privacy
We take a practical, employer-first approach to data governance.
Data Ownership
Customers retain ownership of their data
Functional Use Only
Data is used only to deliver platform functionality
No Unauthorized Use
No resale or unauthorized use of candidate or employer data
Role-Based Access
Role-based access controls and permissions

Compliance
Security & Compliance Maturity
Picsume operates with SOC 2–aligned security controls, including access management, system monitoring, and change management.
SOC 2 Type II Compliance
We are actively working toward SOC 2 Type II compliance, with a target completion in 2026.
Our approach focuses on building durable security practices that reflect how the platform is actually designed and operated — not treating compliance as a checkbox.
Enterprise
Enterprise Security Options
For organizations with stricter requirements, Picsume can provide additional isolation, including:
Dedicated databases
Data-layer isolation
Complete separation of your data at the database level for enhanced security and compliance requirements.
Dedicated environments or deployments
Infrastructure-layer isolation
Fully isolated deployment environments with dedicated infrastructure for maximum control and security.
Built with Trusted Programs & Technology
Picsume participates in leading security, technology, and innovation programs that support continuous improvement.



Questions or Security Reviews?
We’re happy to support security, IT, and procurement conversations with clear, practical explanations of our approach.
Contact Us